In today's digital landscape, phishing scams have emerged as one of the most significant security threats to businesses. Recent statistics reveal that a staggering 83% of organizations experienced successful phishing attacks last year, highlighting the alarming prevalence and potential impact of these malicious campaigns. With nearly one-third of phishing emails being opened, the risk of falling victim to such scams is a real concern for businesses of all sizes.
Cybercriminals have adopted a deceptive tactic from ransomware groups to target people and force them to divulge their login passwords, which has only served to exacerbate the problem. This new variety of phishing assaults follows a well-known pattern, usually starting with an email message warning recipients of questionable account activity. Users may be asked to confirm their email address and password by visiting a link included in the email, which may claim that an unauthorized login attempt has been stopped.
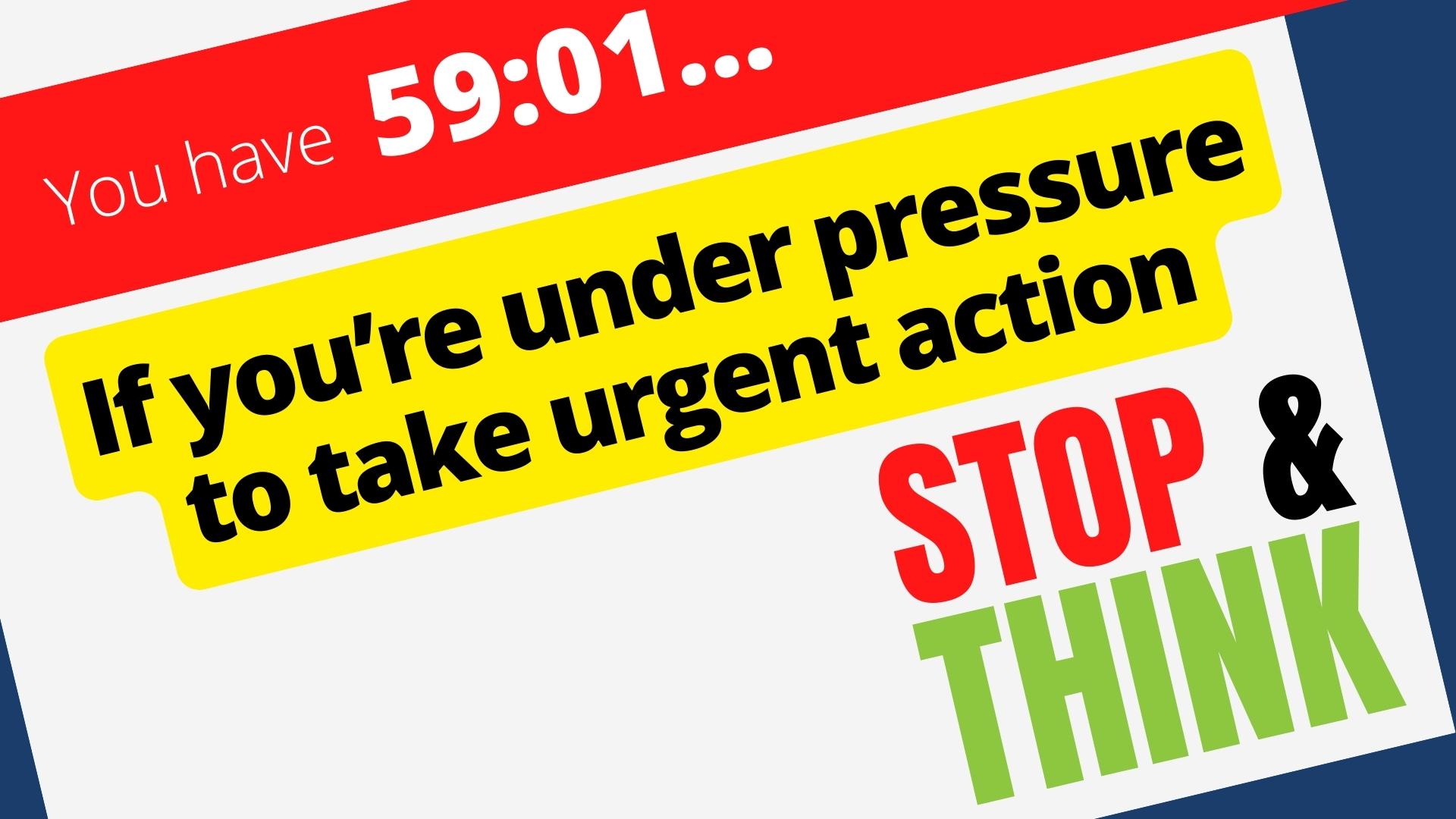
What sets these phishing attacks apart is the inclusion of a countdown timer on the fake webpage. Typically set at one hour, the timer creates a false sense of urgency, compelling individuals to take immediate action. Fear of their account being deleted drives users to overlook crucial signs of a phishing attempt and hastily provide their sensitive information. While the countdown timer may trigger panic, it is crucial to remain vigilant and evaluate the authenticity of such emails before succumbing to the pressure.
Businesses may suffer serious repercussions if they fall for these phishing scams. People inadvertently expose themselves to data theft, financial losses, and malware infections by disclosing login credentials on fake websites. Additionally, using the same password for many accounts raises the danger of compromising other private data. Even worse, compromised login information might be sold on the dark web, opening a door for other cybercriminals to break into more accounts and cause havoc.
To protect your business from phishing attacks, it is essential to implement robust preventive measures. Start by scrutinizing email addresses for any signs of suspicious activity. Pay attention to spelling errors or grammatical mistakes, and hover over links to verify the destination URL. If you suspect you have fallen prey to a phishing scam, immediately change your login credentials but avoid clicking links within the suspicious email. Instead, manually type the website address into your browser to ensure you access the legitimate site.
One effective defense against phishing attacks is the use of password managers. These tools generate strong, complex passwords for each of your accounts, making them virtually impossible for hackers to crack. Password managers securely store these passwords, automatically filling in login fields and effectively detecting fraudulent phishing pages. Encourage your team to adopt this practice to enhance security across the organization.
Defending your company against phishing attacks needs teamwork. Share this article with your entire team to spread awareness of the dangers of phishing attempts and the most effective defenses. Encourage everyone to use caution and seek advice if they ever come across shady sites or emails. Your company may protect its sensitive data and assets by remaining educated and taking preventative measures to stay one step ahead of thieves.
In conclusion, phishing scams pose a significant threat to businesses worldwide. However, by remaining vigilant, implementing preventive measures, and fostering a culture of awareness, you can fortify your defenses and protect your organization from the detrimental effects of these malicious attacks.

0 Comments